Quick filters:
Page 1 of 12
Keylogger Stock Photos and Images
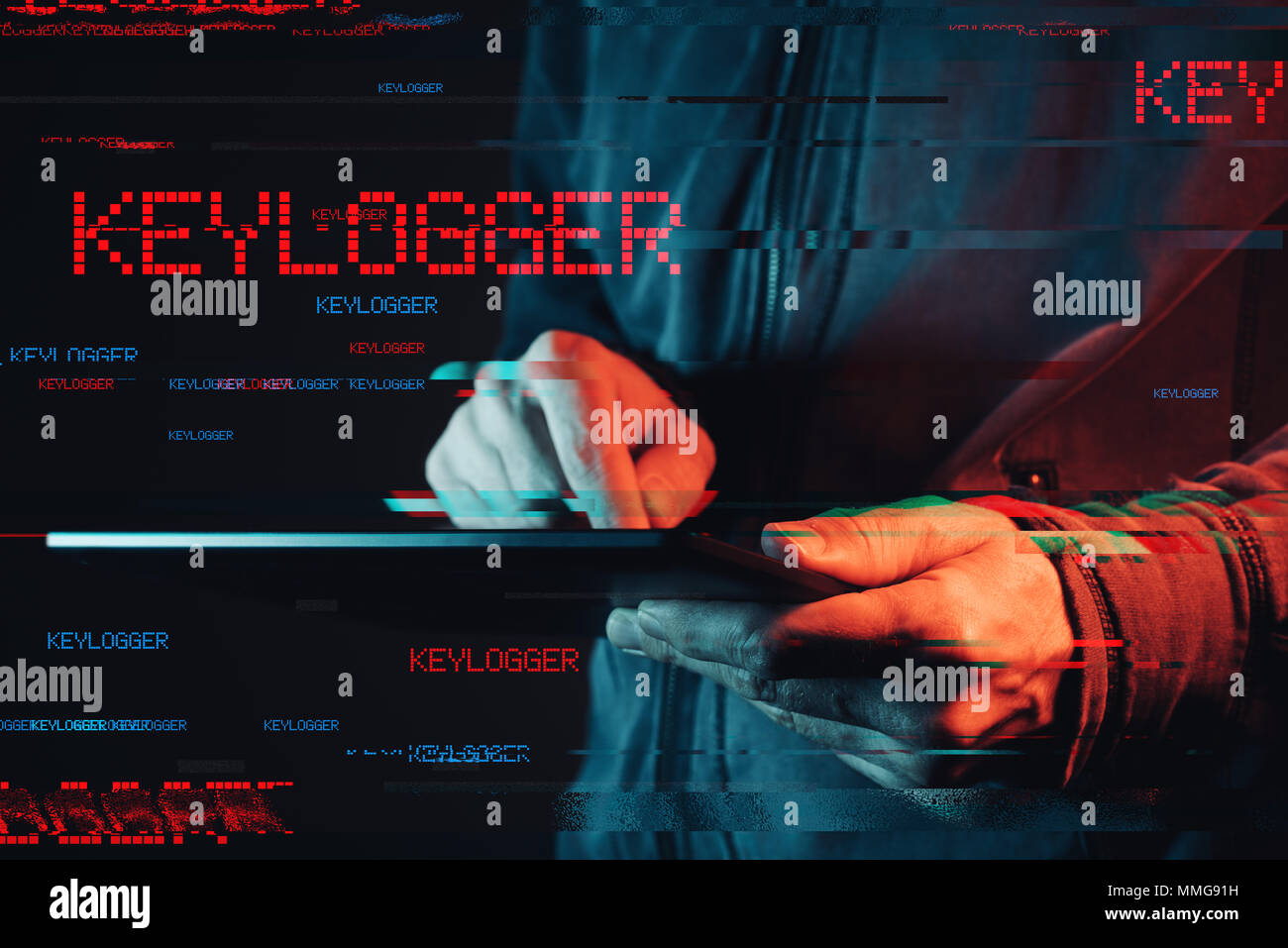
RFMMG91H–Keylogger concept with male person using tablet computer, low key red and blue lit image and digital glitch effect

RFT38M06–Hands typing on laptop keyboard with watching eye on hologram screen. Concept of spy cam, cyber espionage, digital surveillance, spying, hacking, keyl
RF2HNF92G–Keylogger Simple vector icon. Illustration symbol design template for web mobile UI element.

RMK2Y86A–Hacker hacked victim perpetrator computer scam ransom ware terrorist terror anonymous blacked out face
RF2D891HP–Have I Been Pwned (slang for password owned)? Dice form the expression 'pwned? no' or 'pwned? yes'.
RF2H9TGT4–Computer virus concept. Laptop seized by disgusting monster with long sticky tentacles. Data loss danger.
RF2NWC8FC–Black Glasses-Wearing Cybercriminal Hacking in a Dark Room with Mysterious Green Lights, Close-up Shot

RFJRB0YC–Open steel padlock lying on a white computer keyboard in a low angle view in a concpet of privacy and online security
RFMPEFFT–Keylogger concept with male person using tablet computer, low key red and blue lit image and digital glitch effect
RF2HND12Y–Keylogger Simple vector icon. Illustration symbol design template for web mobile UI element.

RFRA114F–Computer virus concept. Laptop with broken screen seized by disgusting monster with long sticky tentacles.
RF2T9WYHG–On a black surface there is a brain and a yellow puzzle with the inscription - DATA LEAK. Science and technology concept.

RF2NWC82M–Black Glasses-Wearing Evil Hacker Hacking Someone on Computer, Looking at Monitors and Performing Hacks
RFMW0C7W–Spyware concept with faceless hooded male person, low key red and blue lit image and digital glitch effect
RFRB41X9–Computer virus concept. Laptop with man inside seized by disgusting monster with long sticky tentacles. Data loss danger.
RF2T980R9–A man inserts a flash drive into his brain with the inscription - DATA LEAK. Science and technology concept.

RFPPF9BW–Woman in the hood sitting and working at laptop as hacker. Running malware program on computer in the internet with malevolent smile on her face.
RFRA114G–Computer virus concept. Notebook with man inside seized by disgusting monster with long sticky tentacles.
RF2T9KW07–On a black surface lies a brain and a yellow puzzle with the inscription - DATA LEAK. Science and technology concept.

RF2NWC15T–Black Glasses-Wearing Hacker Typing on Computer in Dimly-Lit Room with Eerie Green Lighting

RFKNG2GE–Open steel padlock lying on a white computer keyboard in a low angle view in a concpet of privacy

RFR296CM–Woman in the hood sitting and working at laptop as hacker. Running malware program on computer in the internet with malevolent smile on her face
RFRA114H–Cyber security concept. Monstrous computer virus seize system administartor's mug. Laptop with broken screen infected by malware. Data loss danger.

RF2T943WJ–A man inserts a memory card into his brain with the inscription - DATA LEAK. Science and technology concept.
Search Results for Keylogger Stock Photos and Images (1,173)
Page 1 of 12